Tech security expert warns about sim card scam on T-Mobile customers

Cyber-risk expert talks about latest T-Mobile security hack
The bad guys take control. Then they call your phone company and tell them they want to switch your information to a new phone.
FOX 2 - It’s Deja Vu for some T-Mobile customers. In August, hackers exposed 50 million customers' data.
Now there is another issue. The bad guys finding a way to swap your SIM cards.
How scammers take control of your phone number
Cyber risk expert David Derigiotis with Burns & Wilcox explained how it works.
"Your phone essentially goes dead and the attacker ports out your number to their device and now they start receiving all of your calls, all of your text messages," Derigiotis said.
The bad guys take control. Then they call your phone company and tell them they want to switch your information to a new phone.
"The other is, good old-fashioned social engineering," he said. "They called, they trick the individual pretend that they are you. And they’re asking to port out that number and they’re able to simply do that by deceiving and tricking which is social engineering, taking advantage of that human element."
Dangers of SIM card swapping
Here’s the real danger. Many of us have authentication for other programs on our computers tied to our phones. So, think about it. You try to get into a program on your laptop, it pushes an authentication message to the cellphone the crooks now have in their control.
"If you’re using the text message as a second form of authentication for logging into an account whether it be a banking, email, whatever it may be," Derigiotis said. "They got access to that second authentication mechanism. That’s what happened to a number of individuals."
How to protect yourself from T-Mobile scam
So, the best advice, double down on safety around your cell.
"What everyone should do is stop using their cell phone number, stop using that text as a second form of authentication," he said. "Because we see right here, this is the real weak spot, and breaking through that, and being able to get into an online account.
"I think it’s more important to use some type of app-based authentication, they have different forms out there, Google authenticator, Authy, there are also hardware out there where you can plug into the computer and by the computer, and it will present that additional code.
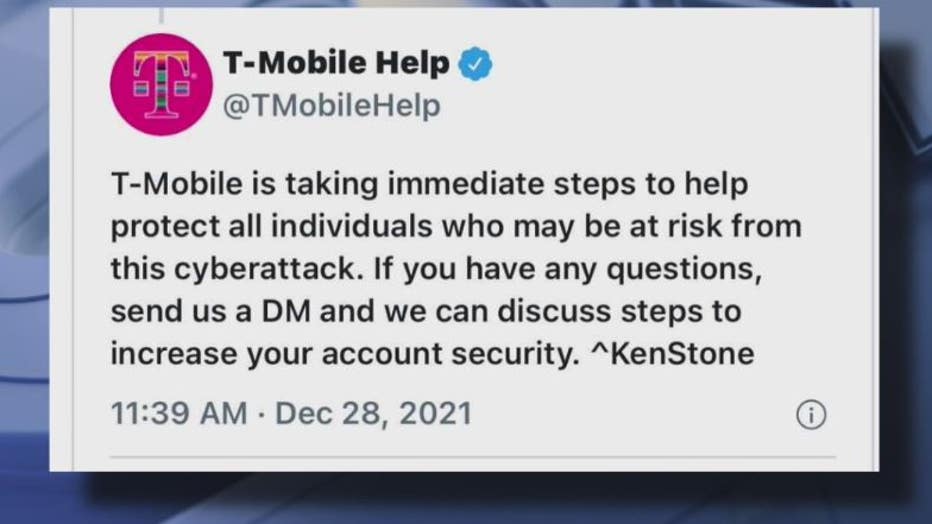
T-Mobile responding to people who were hit by this latest attack saying they’re taking immediate steps to help protect all individuals who may be at risk from this cyberattack.


